Protecting your Business from Insider threats
Insider threats can pose a serious threat to your business due to their access to sensitive information and critical assets. In this blog post, we will share the different categories, types and how you can best defend your business from a successful insider attack.
What is an Insider Threat?
An insider threat is anyone who is or was working for your organization and poses a risk to the stability and security of your organization. Third-party contractors can also be insider threats. For insiders that turn malicious, researchers have found that the acts are rarely spontaneous and are usually the result of a deliberate decision.
Insider Threat Categories
Insider threat actors come in many forms. Here are the most common categories to be aware of:
Sabotage: The insider uses their legitimate access to damage or destroy your organization's computer systems or data.
Fraud: Theft, modification, or destruction of data for the purpose of deception or financial gain by the insider.
Theft: When an insider steals your organization's intellectual property or financial assets, often for resale or to take with them to a new position.
Espionage: When an insider secretly collects information for another organization, such as a government or competitor, for their benefit.
Types of Insider Threats
In addition to insider threat categories, there are also many different types of threats. Regardless of their intent, bad actors can do serious damage to your business. Here’s some of the different types of threats business leaders need to be aware of:
Malicious Insiders: Those that may believe they’ve been wronged by your organization and decide to act on it. These acts are intentional and may include leaking or deleting sensitive information or other types of sabotage.
Negligent Workers: Acts of negligence within an organization are more common than malicious acts and pose an equally severe risk. Actions such as unintentionally leaving a laptop unlocked while working remotely can have serious consequences.
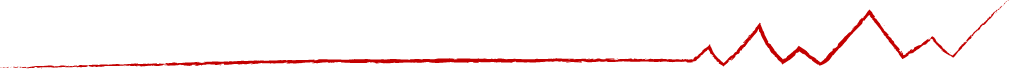
Insider threats are trending upward in Canada making employee training, upskilling, and oversight the lynchpin to a well-rounded cybersecurity strategy. - KPMG
Departing Employees: Any employee leaving your organization, for any reason, can pose a major threat by stealing sensitive data, stealing intellectual property, or committing other harmful acts.
Security Evaders: Some employees may find security policies to be overwhelming at times. Because of this, the average employee may take steps to avoid critical security controls. Circumventing these controls may put your organization at a higher risk of a cyber incident.
Inside Agents: If an outside group targets your organization, they may use the unique privileges of an employee to their advantage. The employee involved may be tricked or compelled through bribery or blackmail to act as an insider threat.
Third Party Partners: External vendors, contractors, and consultants may also be given access to sensitive data and may not always have your company’s best interest in mind.

Unintentional Harm: Employees make mistakes that may also lead to serious consequences for your organization. These unintentional actions might happen, but it's important to follow processes and procedures to minimize this risk.
It's impossible to completely eliminate the risk of insider threats. With a Managed Services Provider, you can prioritize hardening your security posture, protect your data and have monitoring and alerting processes in place to identify any unusual activity. Here are some of the ways to mitigate insider threats:
Technical Controls: Help prevent an insider threat from causing harm by stopping the action through technical means, such as computer auto-lock out or disabling a door access.
Procedural Controls: Workplace policies every business should have in place that may, for instance require employees to never share sensitive information or harm the organization, but typically aren't enough to stop a motivated insider threat.
Always Alert: Identifying suspicious behavior is important to protect your organization. Ensure you have a communication process in place to immediately report suspicious activity to the appropriate personnel.
Everyone in your organization relies on each other to stay secure. Employees need to be informed of risks and technical and procedural controls should be in place to mitigate the risks of insider threats. Security best practices, such as Security Awareness Training can also help to mitigate internal threats. To learn more about our Managed Security Services, visit our website or contact us.